About
I work with founders and teams that need senior engineering without the overhead of a full hire. Most of what I ship is infrastructure-adjacent: security tooling, data pipelines, internal platforms, and the occasional customer-facing product.
I've worked across crypto, cyber-security, HR-tech, and intelligence. I treat LLMs as a power tool, not a product category — they go where they measurably cut work, and nowhere else.
Services
-
Web applications
Dashboards, admin tools, internal platforms. React or plain TypeScript on the front; Go, Node, or Python on the back.
-
Scraping & data migration
Legacy extractions, structured pipelines, deduping across schemas — at scale, without surprises.
-
LLM-backed features
Retrieval, classification, extraction, agentic workflows. Evaluated, not vibed.
-
Security engineering
Compliance scanners, hardening tooling, threat-surface review for cloud and on-prem.
Selected Work
A small sample.
-
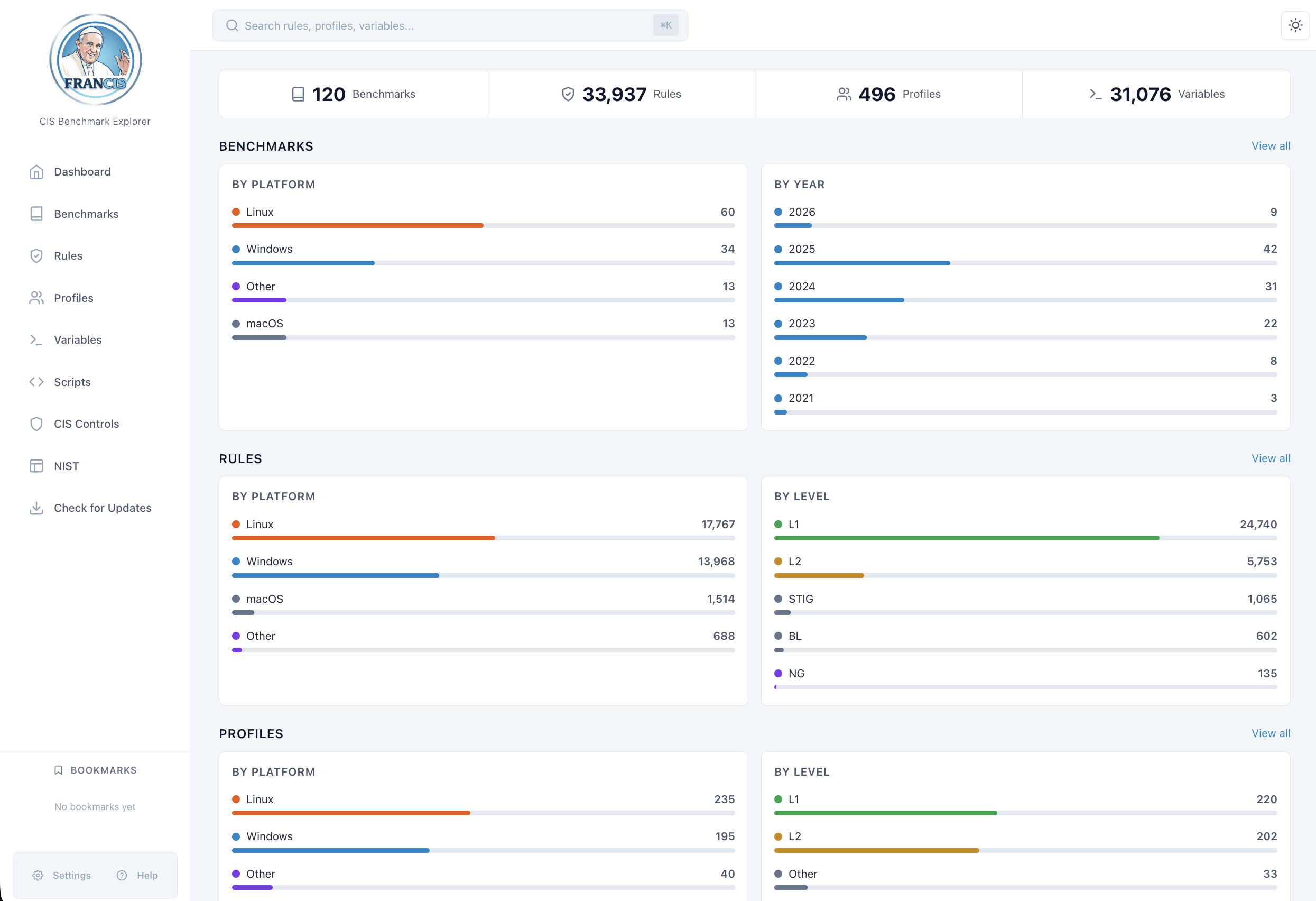
Compliance benchmark explorer
A browsable atlas for thousands of CIS rules across 120+ benchmarks — indexed, cross-linked, and served sub-100ms.
- TypeScript
- React
- Node
- PostgreSQL
-
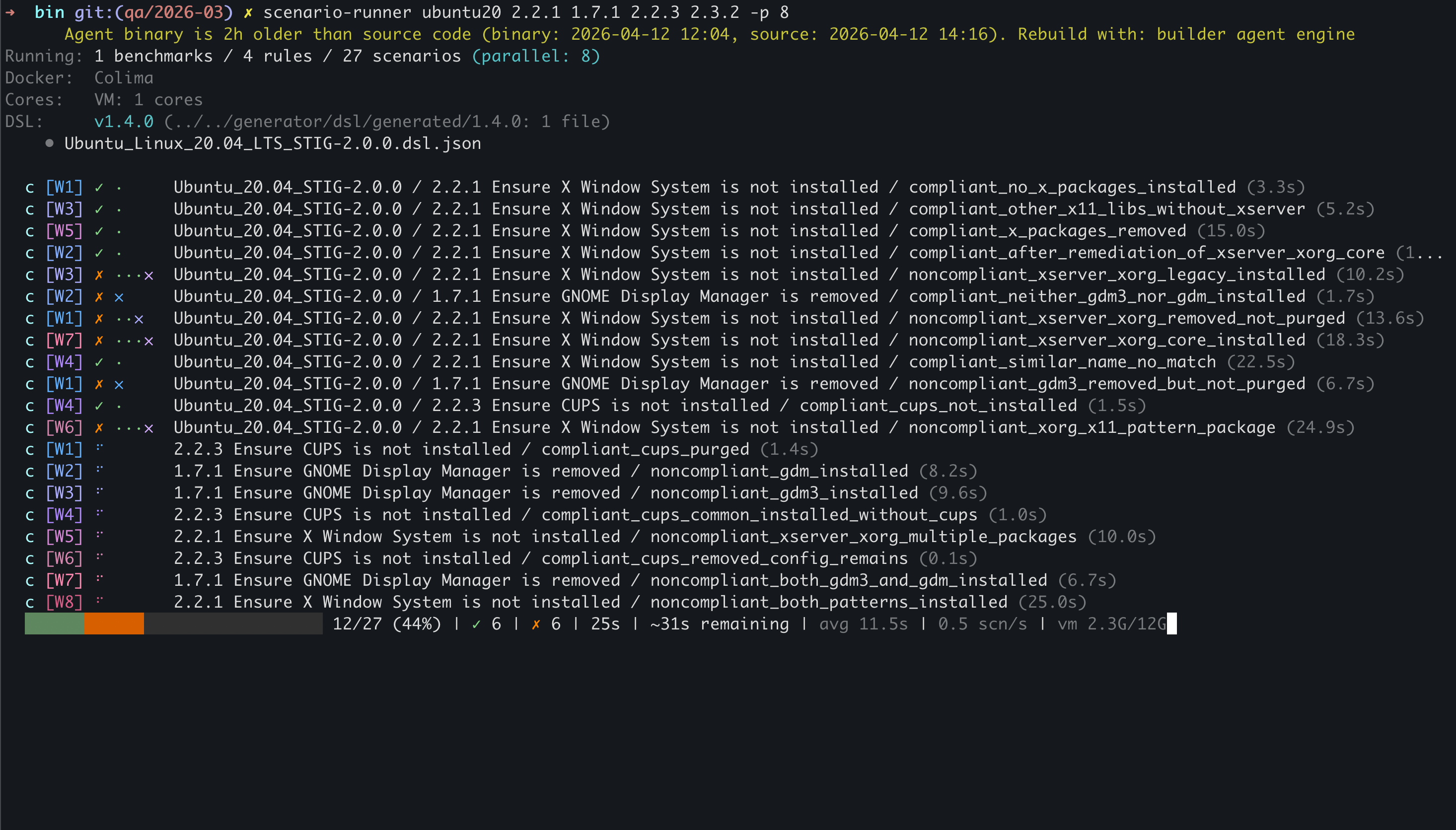
Security scanner CLI
A compliance-test harness with a live TUI: provisions VMs, runs scenarios in parallel, reports pass/fail across Ubuntu and RHEL hardening rules.
- Python
- Docker
- Lima
- TUI
- LLM
Previously
A few of the places I've done my work.
-
2026 — Present
Remedio
Freelance engineering
- Python
- Go
- PostgreSQL
- Claude
-
2022 — 2025
Solidus Labs
Crypto compliance & market surveillance
- Go
- Python
- Kafka
- Redis
- Snowflake
-
2021
Linx Security
Identity security & ETL
- Python
- AWS
- MongoDB
- ArangoDB
-
2016 — 2017
Armis
Asset visibility & security
- Python
- MongoDB
-
2015 — 2016
SafeBreach
Breach & attack simulation
- Node.js
- Docker
Stack
- Go
- Python
- TypeScript
- Node
- React
- Rust
- SQL
- PostgreSQL
- MongoDB
- Redis
- Kafka
- Docker
- Kubernetes
- AWS
- LLMs
At scale
- Realtime ETL pipelines moving billions of rows.
- Compliance catalogs indexing tens of thousands of security rules.
- Identity platforms stitching together multiple legacy auth providers.